Void DEX
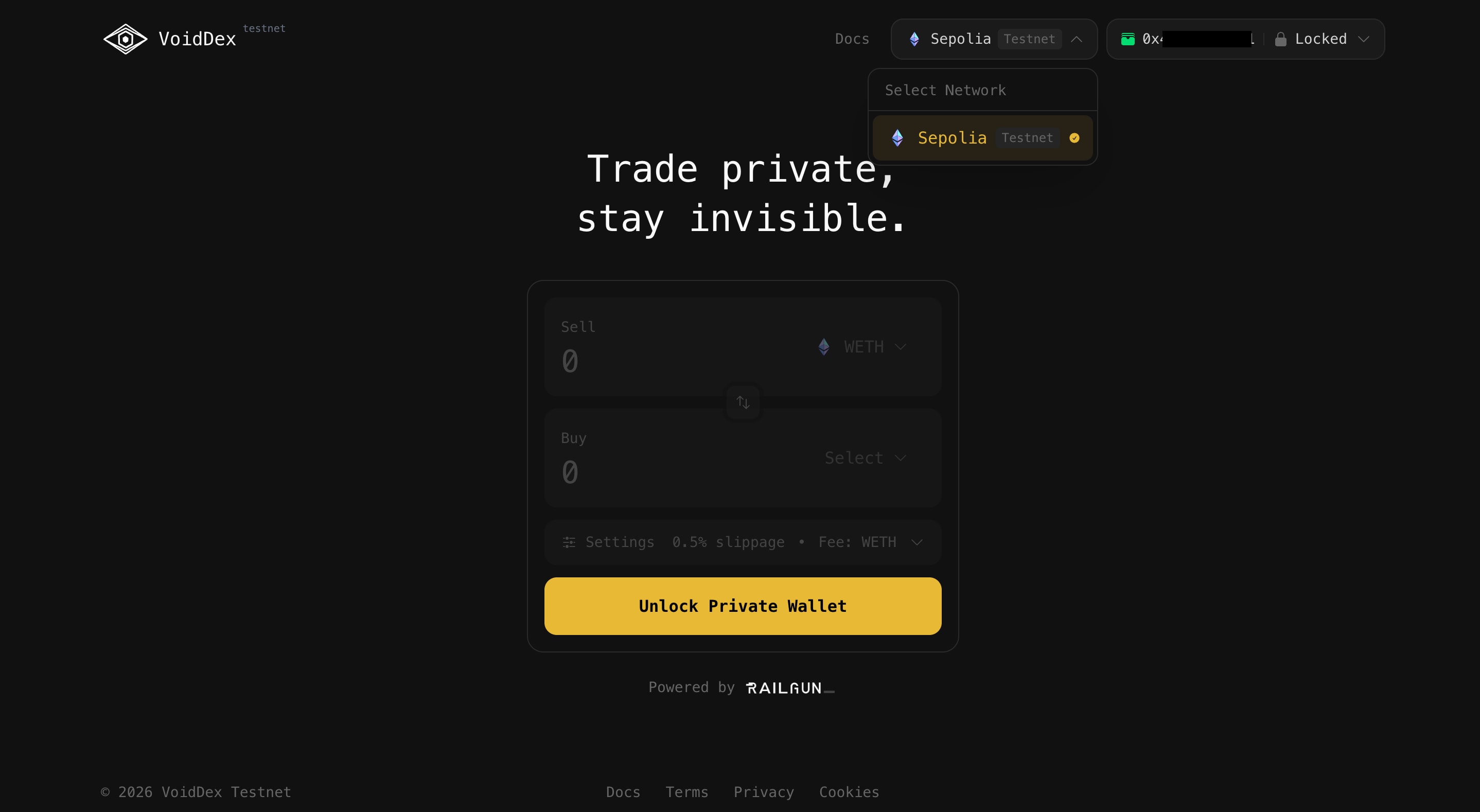
Privacy-first DEX aggregator that combines best swap rates with Railgun's zero-knowledge privacy technology.
## Void DEX
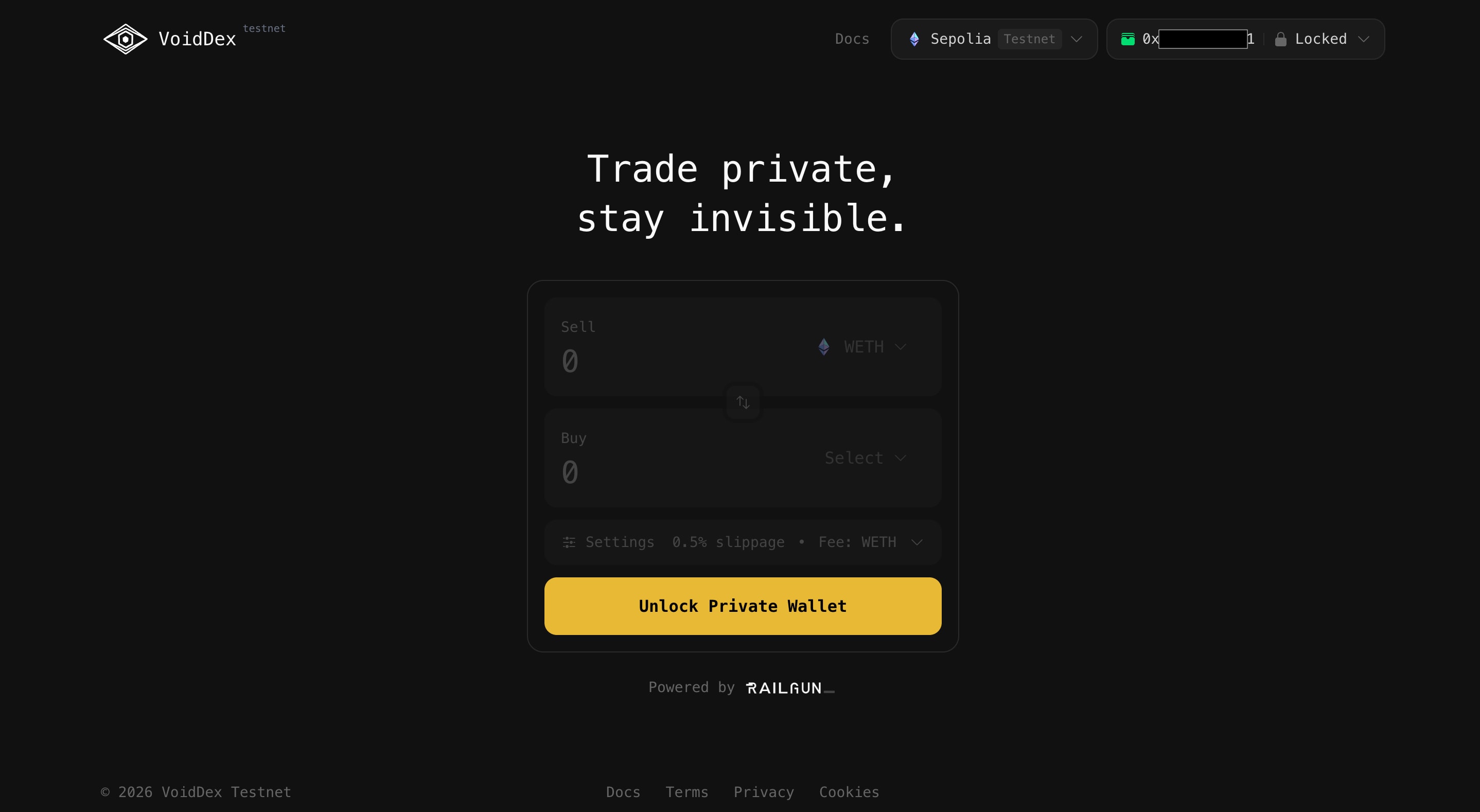
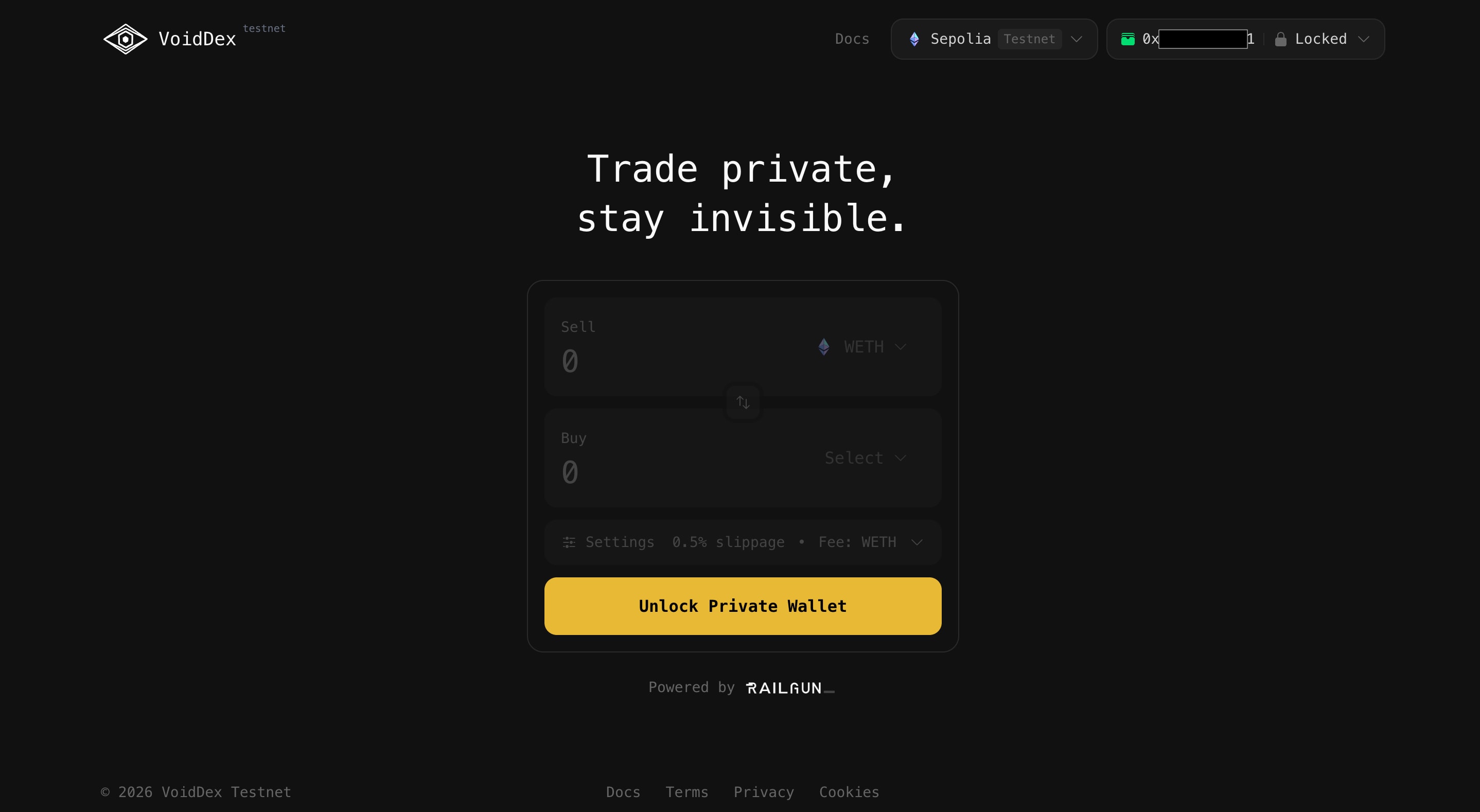
Every transaction on a public blockchain tells a story. When you swap tokens on a decentralized exchange, that story is broadcast to the world: your wallet address, the tokens you hold, the amounts you're moving, and every address you've ever interacted with. For many users, this level of transparency isn't just uncomfortable, it's a genuine security risk. Void DEX was built to solve this fundamental tension between DeFi's openness and users' legitimate need for financial privacy.
Void DEX is a privacy-first DEX aggregator that combines optimal swap rates across decentralized exchanges with Railgun's zero-knowledge privacy technology. At its core, the system operates on one non-negotiable principle: **your wallet keys never leave your browser**. Every privacy-critical operation, from generating zero-knowledge proofs to decrypting your private balance to signing transactions, happens entirely on the client side using Railgun's zkSNARK system compiled to WebAssembly.
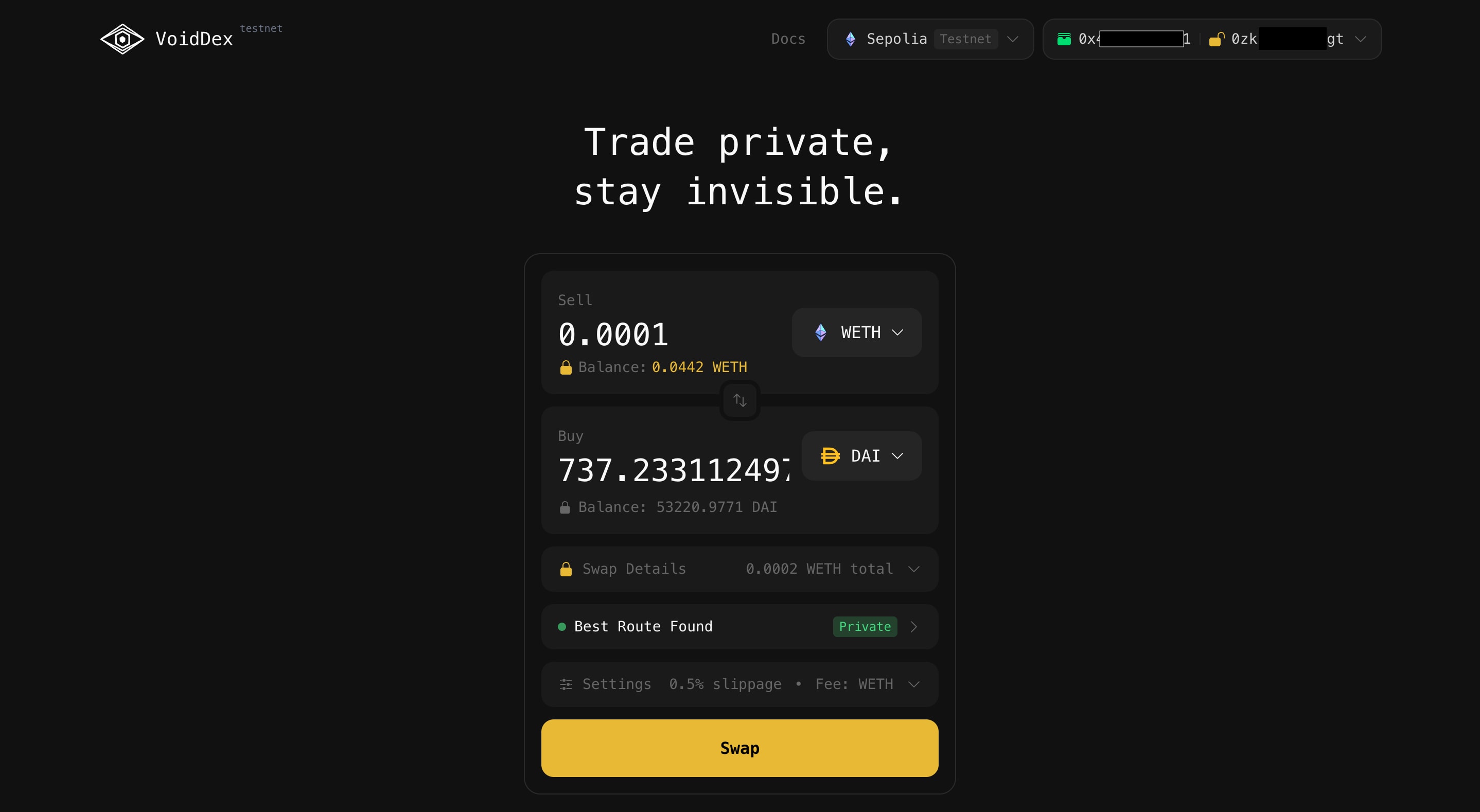
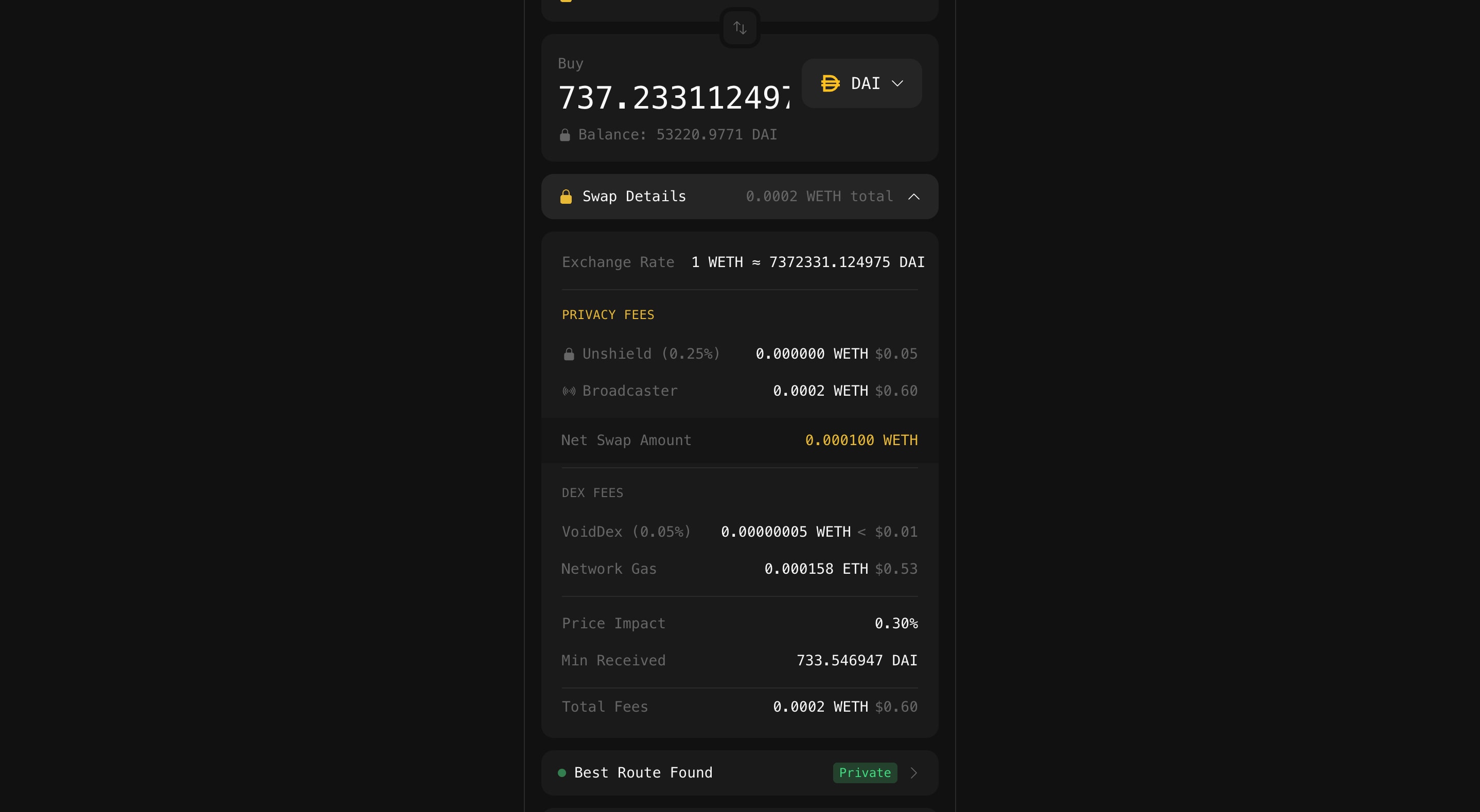
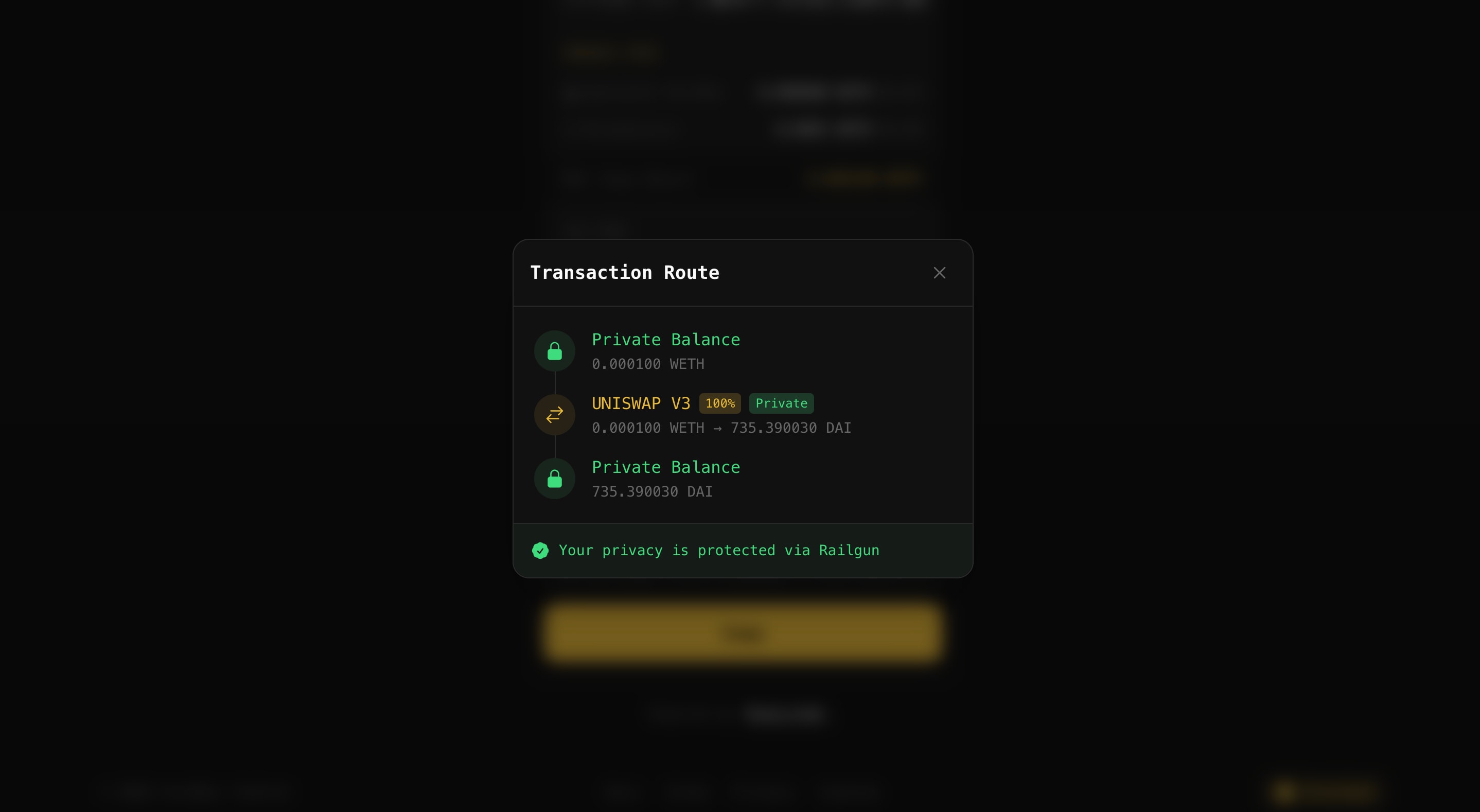
The result is a trading experience where you get the best available rates across multiple DEXes while keeping your financial activity private. The aggregator queries Uniswap V2 and V3 pools to find optimal routes, intelligently splits large orders across venues when beneficial, and then executes the entire swap through Railgun's privacy layer. To external observers, including VoidDex's own servers, the connection between your public wallet and your trading activity remains cryptographically hidden.
## Tech Stack
| Layer | Technologies |
|-------|-------------|
| Frontend | Next.js, React, Wagmi, RainbowKit, Railgun SDK |
| Backend | NestJS, PostgreSQL, Redis |
| Smart Contracts | Solidity, Foundry, OpenZeppelin |
| Privacy | Railgun, zkSNARKs, Waku P2P |
## Architecture Overview
The architecture of Void DEX reflects a deliberate security choice: the system is split between a privacy-sensitive client layer and a privacy-agnostic server layer. Your browser runs the complete Railgun SDK, which manages your private keys, generates zero-knowledge proofs, and decrypts your shielded balance. The server, by contrast, only handles public data. It queries DEX contracts for price quotes, maintains token lists, and caches market data, but it never touches anything that could compromise your privacy. When you initiate a swap, the server prepares an unsigned transaction with the optimal route, but it's your browser that generates the ZK proof and signs the final transaction. This means even a fully compromised server couldn't steal funds or reveal your private trading history.
```mermaid
flowchart TD
User[User]
User --> Browser
subgraph Browser[Your Browser]
Frontend[VoidDex UI]
SDK[Railgun SDK + Keys + ZK Proofs]
end
subgraph Server[VoidDex Server]
API[API - Quotes, Tokens, Prices]
end
subgraph Blockchain[Blockchain]
DEX[DEX Contracts]
Router[VoidDex Router]
Railgun[Railgun Contracts]
end
Frontend --> API
API --> DEX
SDK --> Railgun
Railgun --> Router
Router --> DEX
```
### Client vs Server
| Component | Location | Data Handled |
|-----------|----------|--------------|
| Private Keys | Browser | Never transmitted |
| ZK Proofs | Browser | Generated locally |
| Balance Decryption | Browser | Only you can see |
| Swap Quotes | Server | Public price data |
| Token Lists | Server | Public token info |
## How It Works
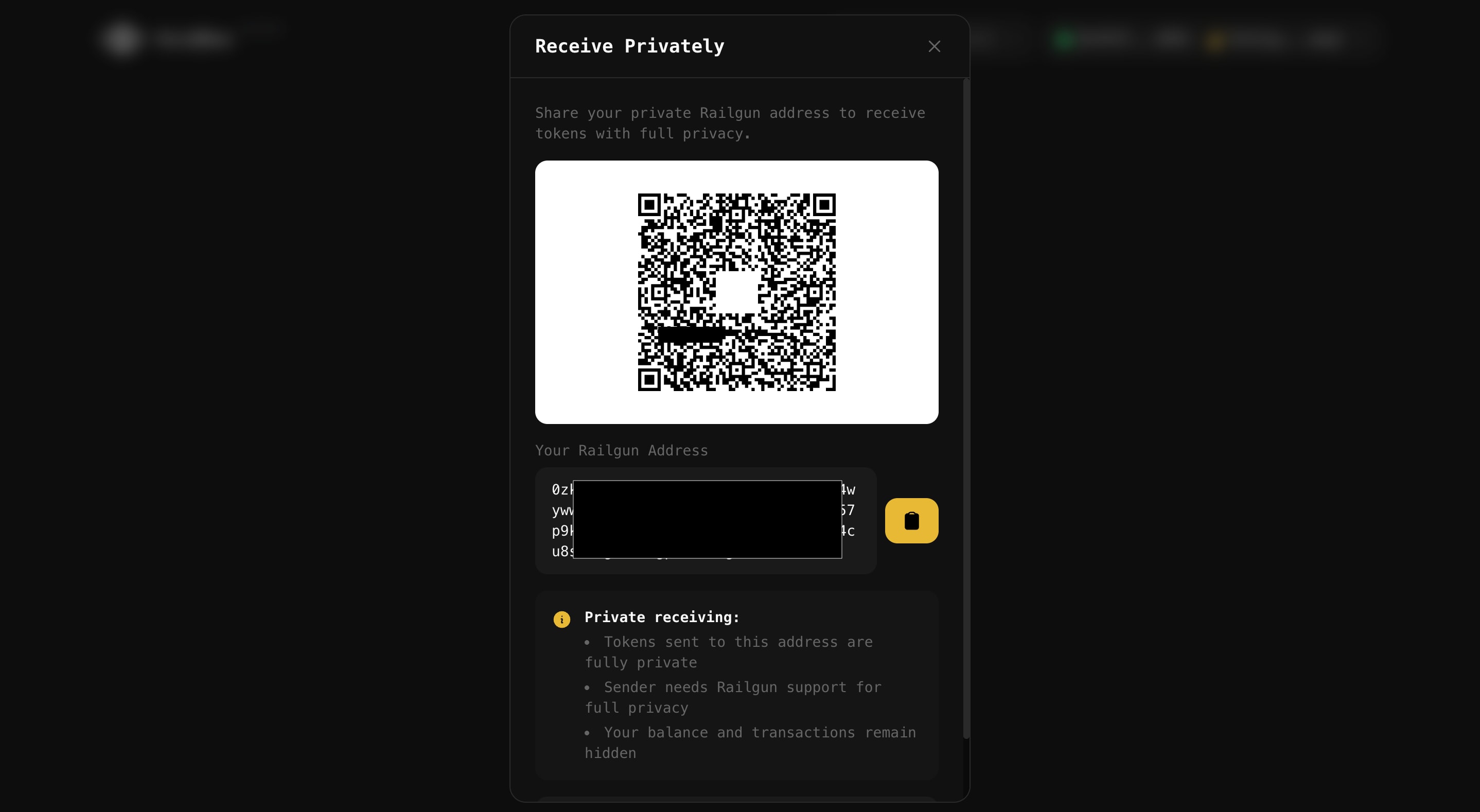
Privacy in Void DEX revolves around the concept of shielding and unshielding tokens. When you shield tokens, you deposit them into Railgun's smart contract, which converts them into private UTXOs (unspent transaction outputs) that only you can see and spend. Your private balance exists as encrypted notes on-chain. Only someone with your viewing key, which never leaves your browser, can decrypt and see what you own. When you want to exit the private pool, you unshield tokens to any public address, breaking the on-chain link between your original deposit and the withdrawal.
The magic happens in between. While your tokens are shielded, you can swap them privately through Void DEX. The Railgun SDK, running entirely in your browser, generates a zero-knowledge proof that demonstrates you have sufficient balance to execute the swap without revealing which specific UTXOs you're spending. This proof is then broadcast through Waku, a decentralized peer-to-peer network, ensuring even transaction submission doesn't rely on centralized infrastructure.
```mermaid
flowchart TD
A[Public Tokens] --> B[Shield]
B --> C[Private Balance]
C --> D[Private Swap]
D --> C
C --> E[Unshield]
E --> F[Public Address]
```
When you execute a private swap, the following sequence occurs:
1. Your browser generates a zero-knowledge proof using the Railgun SDK
2. The proof cryptographically demonstrates sufficient balance without revealing which UTXOs you own
3. The signed transaction is broadcast through the Waku P2P network
4. Railgun's smart contract verifies the proof and calls VoidDex Router as an "adapt contract"
5. The Router executes the swap through the appropriate DEX adapters
6. Output tokens are automatically re-shielded back to your private balance
## Smart Contract Design
The VoidDexRouter contract is designed around flexibility and composability. Rather than hardcoding support for specific DEXes, the router uses a modular adapter system where each DEX integration is a separate contract identified by a unique `dexId`. This allows the system to support new DEXes without upgrading the core router. The router exposes three distinct swap modes to handle different trading scenarios: simple single-DEX swaps for straightforward trades, split routing that divides a trade across multiple venues in parallel for better execution on large orders, and sequential multi-hop routing for trades that need to go through intermediate tokens (like swapping a long-tail token through ETH to USDC).
```solidity:src/VoidDexRouter.sol
// Single swap parameters
struct SwapParams {
address tokenIn;
address tokenOut;
uint256 amountIn;
uint256 minAmountOut;
bytes32 dexId;
bytes dexData;
}
// Split routing step (parallel execution)
struct RouteStep {
bytes32 dexId;
uint256 percentage; // 10000 = 100%
uint256 minAmountOut;
bytes dexData;
}
// Sequential hop (A->B->C routing)
struct SequentialStep {
bytes32 dexId;
address tokenOut;
uint256 minAmountOut;
bytes dexData;
}
```
These structs enable powerful routing strategies while keeping gas costs reasonable. The `SwapParams` struct handles the common case of a direct swap through a single DEX. The `RouteStep` struct enables parallel execution where a percentage of the input amount flows through each route, useful when splitting a large order across Uniswap V2 and V3 for better price impact. The `SequentialStep` struct chains multiple swaps together, carrying the output of one hop as the input to the next. The `dexData` field in each struct provides a generic way to pass DEX-specific parameters like pool addresses, fee tiers, or custom routing hints.
## Security Model
The security architecture of Void DEX starts from a simple premise: assume the server will be compromised. By designing the system so that all sensitive operations happen client-side, a breach of VoidDex's infrastructure cannot compromise user funds or reveal private trading activity. The server exists purely to aggregate public market data and prepare unsigned transactions. It never sees your private key, your Railgun viewing key, your decrypted balance, or which UTXOs belong to you. Even the act of transaction signing happens in your browser, not on any server.
| Component | Location | What This Means |
|-----------|----------|-----------------|
| Private Key | Browser only | Never transmitted, never stored on server |
| Railgun Viewing Key | Browser only | Only you can see your private balance |
| ZK Proof Generation | Browser (WASM) | Proofs created locally, server can't forge them |
| Balance Decryption | Browser only | Server has zero knowledge of your holdings |
| Transaction Signing | Browser only | Server prepares unsigned TX, you sign locally |
On the smart contract side, the VoidDexRouter implements defense-in-depth with multiple security layers:
- **Access Control**: Role-based permissions separate Admin, Operator, and Guardian capabilities
- **Pausability**: Guardian role can pause the contract immediately in emergencies
- **Reentrancy Guard**: All external calls are protected against reentrancy attacks
- **SafeERC20**: Handles non-standard token implementations that don't return booleans
- **Slippage Protection**: Minimum output amounts are enforced on-chain, not just off-chain
## More Slices From This Pzza
Dive deeper into the ideas and technology behind this project:
- [Privacy Architecture in VoidDex: Integrating Railgun's zkSNARK System](/oven/voiddex-privacy-architecture-railgun) - How VoidDex implements private token swaps using Railgun's zero-knowledge proof system
- [VoidDex Router: Designing a Multi-DEX Swap Router with Split Routing](/oven/voiddex-smart-contract-router-design) - Deep dive into the smart contract architecture, DEX adapter system, and split routing
- [DEX Aggregation in VoidDex: Building an Optimal Route Finder](/oven/voiddex-dex-aggregation-routing) - How the backend finds the best swap routes across multiple DEXes